|
This section addresses the following questions:
|
Before you begin worrying about the individual methods of risk management, you need to be clear that there is no "one size fits all" method for all application areas. For example, there are some methods that deal primarily with risk identification (e.g. fault tree analysis = FTA), and other methods which concentrate more on the evaluation of errors and determination of risk-minimising measures (e.g. Failure Mode Effects Analysis = FMEA).
A large number of publications are available that provide information about and descriptions of the various methods of risk management (more information is contained in (chapter E.8 ICH Q9: Quality Risk Management ). The methods referred to in this chapter are taken from ICH Q9 Quality Risk Management (see chapter E.8 ICH Q9: Quality Risk Management ) . This guideline contains one of the most comprehensive lists. It is also one of the most recent guidelines in this field, and therefore reflects the current state of the art. Furthermore, greater emphasis is placed on the informal method which, although not explicitly listed in Q9, is of great importance due to its flexible and simple applicability.
In this method, the saying less is more also applies, i.e. the number of methods used for recording and evaluating the risks should be limited to facilitate comparisons between similar processes and the use of synergies, as well as to ensure that the training required remains within reasonable limits.
Annex 1 of ICH Q9 lists nine methods for the execution of risk management. It is important to note that the first method is not a risk management method in the true sense, but provides options for fulfilment of the necessary prerequisites in terms of process/product knowledge, understanding, and transparency. All further methods build on this.
Methods of risk management acc. to ICH Q9, Annex 1:
1. Basic risk management facilitation methods
2. Failure Mode Effects Analysis (FMEA)
3. Failure Mode Effects and Criticality Analysis (FMECA)
4. Fault Tree Analysis (FTA)
5. Hazard Analysis and Critical Control Points (HACCP)
6. Hazard Operability Analysis (HAZOP)
7. Preliminary Hazard Analysis (PHA)
8. Risk ranking and filtering
9. Supporting statistic tools
1 Application areas of selected methods
Thorough preparation for the risk management process is essential (see chapter 10.A.1 Objectives and advantages of risk management). The methods described below can only be usefully and effectively applied once this has taken place.
|
Focus |
Methods |
FTA |
FMEA |
HACCP |
Statistical methods |
|---|---|---|---|---|---|
|
Risk assessment |
Risk identification |
+ |
o |
o |
+ |
|
Risk analysis |
o |
+ |
o |
+ |
|
|
Risk evaluation |
- |
+ |
o |
+ |
|
|
Controlling risks |
Risk reduction |
- |
+ |
+ |
- |
|
Risk acceptance |
- |
+ |
+ |
- |
|
|
Risk review |
o* |
||||
|
Risk communication |
|||||
|
* In order to evaluate whether the planned measures have led to the expected success, additional instruments must be implemented that are suitable for the particular problem. This means that none of the methods mentioned here is suitable on its own. (+ = very suitable, o = limited suitability, - = not suitable) |
|||||
The procedure that can be implemented most simply and universally is an informal approach (chapter 3 Informal method), in which the circumstances, alternative options and their effects/risks are documented, together with a conclusion. Figure 1 provides an overview of the application emphasis of the most important formal risk management methods. Depending on the characteristics of each method, the weak points of individual methods can be compensated by supplementary/supporting activities. The focus is selected according to the risk management process from ICH Q9.
Figure 1 provides an initial indication of the focus points of the individual methods, and should not be interpreted as a definite specification. This means that risk communication can be guaranteed for all methods, e.g. through suitable organisational measures and processing of information. The only difference is that certain methods (e.g. HACCP) also include this risk communication in their theoretical approach.
Statistical methods offer an important instrument for the assessment of product and process quality and for the identification and evaluation of risks, as well as the visualisation and reduction of these risks. For detailed descriptions of the individual methods, refer to the relevant literature on the subject.
|
Summary Since there is no single method suitable for all application areas, in practice, risk management will always be composed of several methods. In order to keep the training effort to a minimum and to maximise the use of synergies, companies should still limit the number of different methods used (max. 3-4). The ICH Q9 Quality Risk Management guideline provides an overview of the most commonly applied methods in the pharmaceutical industry. |
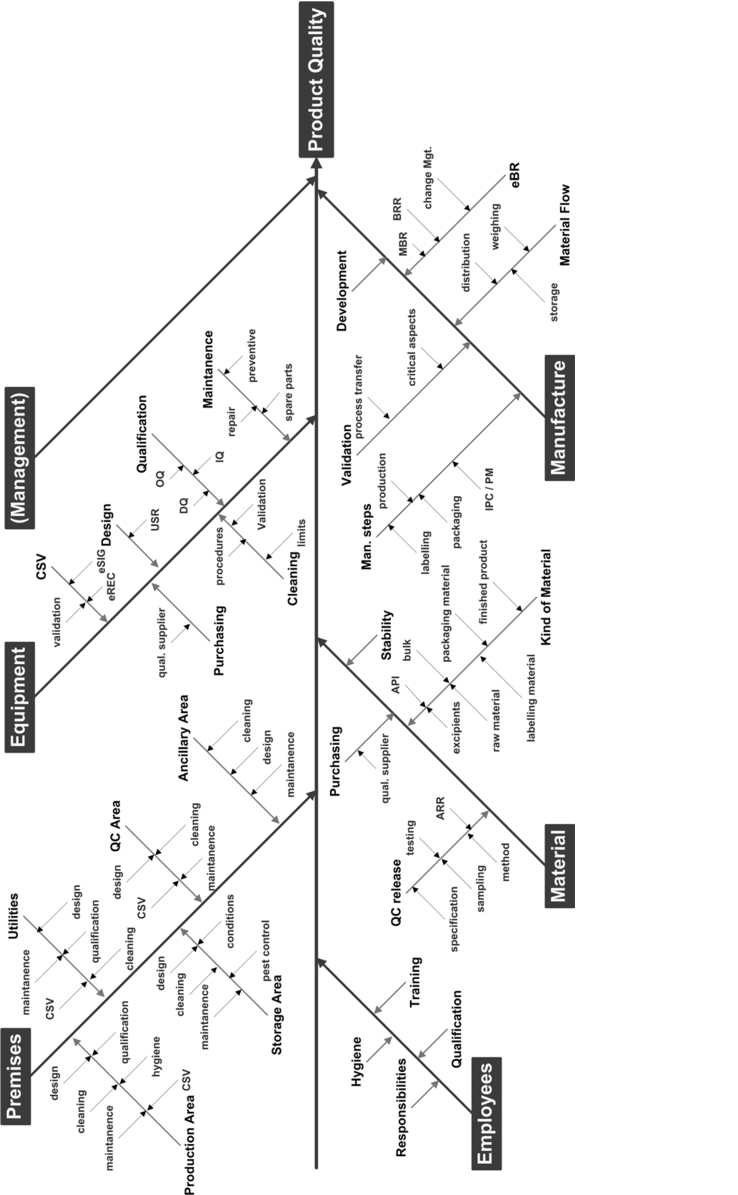
2 Preparation using a fishbone diagram
The fishbone diagram tool was developed by Kaoru Ishikawa (1915-1989) for purposes of quality improvement (cause and effect diagram, see figure 2). It is based on the five Ms (Manpower, Methods, Materials, Machinery, and Milieu) and is used to observe and visualise cause/effect relationships in "problem awareness processes". This diagram is one of the so-called seven pillars of quality management and is often used as a starting point for working and learning processes with an organisational focus. The diagram begins with a horizontal arrow pointing to the right, representing the backbone of the fish. The problem is formulated as concisely as possible at the head. The cause groups (5 Ms) then extend upwards and downwards along this main spine. A variety of creativity techniques are used to identify the cause of the individual problems.
The summarisation of all critical influencing variables in a fishbone diagram provides a very useful instrument for the identification of possible failures, and for representing the causal relationships.
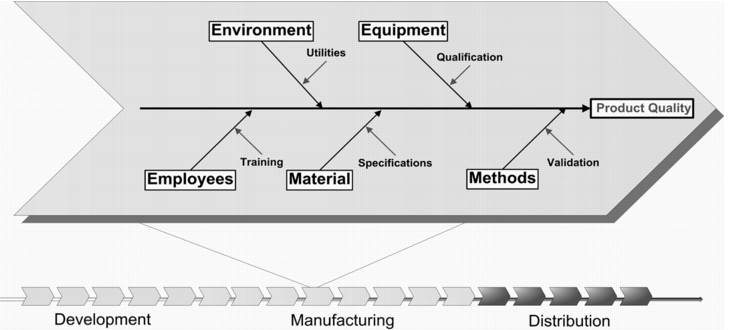 |
Starting from the question "Which factors can influence the quality of the product?", the main branches are formed as follows:
- Manpower
- Machinery, e.g. equipment in direct contact with the product
- Materials
- Methods, e.g. manufacturing process
- Milieu (environment) e.g. all support and supplementary facilities that are required for manufacturing
- Sometimes, the diagram also includes management as an influencing factor.
The outcome of a fishbone diagram can provide a systematic overview of potential critical variables and can be used as a basis for an FTA or FMEA.
2.1 Instructions for execution
A fishbone diagram can be created in three steps:
Step 1:
- Sufficiently detailed description of the system or process
- Definition of the interfaces to neighbouring systems or processes
- Identification of responsibilities and competences.
Step 2:
Starting from the five main branches of manpower, machinery, materials, methods, and milieu (environment), all aspects and influencing variables are determined that may be relevant for the balance sheet classification. The result is a fishbone diagram that forms a basis for the identification of critical variables in the manufacturing process. This overview can be used as a checklist.
 |
Step 3:
Once the critical variables have been established, an FTA or FMEA can be performed immediately in order to evaluate risks and derive appropriate corrective measures. Figure 3 shows an example of possible factors influencing quality in the manufacturing area.
2.2 Advantages and disadvantages
One advantage is that all influencing variables are displayed systematically and must be worked out in a team. A disadvantage is a possible risk of losing sight of the overview effect when studying more complex systems.
3 Informal method
|
This chapter addresses the following questions:
|
On close examination, every decision is subject to a risk evaluation, whether conscious or subconscious. This takes place inside the head of the decision maker and is based on their experience, knowledge, and/or a decision-making template, which generally contains details of the current circumstances, several alternatives and a recommendation.
This is precisely where the informal method applies - but the difference here is that the process which normally takes place inside the head of the decision maker, is instead informally documented. This documentation normally includes:
- A description of the circumstances and outline conditions as well as a question (formulated as concisely as possible)
- A brief list of possible alternatives or solutions
- An assessment of the possible risk ("What could happen, if ..." or "What could happen, if.. not...")
- A recommendation for the decision
- The decision itself
- Signatures (at least from a member of quality assurance and the decision maker), if this risk evaluation is/will form a part of any official GMP documentation)
3.1 Example
During the validation process of computerised systems, the question arose as to whether the import of up-to-date virus scanners automatically via the central IT department would influence the validation status of GMP-relevant applications. The relevant risk analysis was compiled and is provided in the example below.
In the first section, the circumstances (as the reason behind the risk analysis), the scope, and the summary are described.
- Purpose: This document describes a general risk evaluation with reference to the automatic import of security hot fixes and virus scanners in the GMP environment.
- Scope: This risk evaluation can be used for all systems in the GMP environment that are supervised by [...].
- Summary: On the basis of a risk evaluation, the automatic import generally guarantees a higher level of security. The risks in terms of GMP compliance are low, as long as a defined procedure is complied with.
The actual risk evaluation then follows, in this case with two possible alternatives (figure 4).
In this case, for the (preferred) alternative A, the conditions are also specified under which the residual risk is acceptable. Corresponding measures for risk reduction are also specified
For alternative B, a statement for risk reduction is required (which ultimately also contributes to the decision), but this is not possible here.
|
Alternative A: |
Alternative B: |
|
|---|---|---|
|
Security hot fixes and virus scanners are implemented via an automatic update service. |
No automatic implementation. Instead, updates are implemented on demand with a certain time delay. |
|
|
Risk analysis |
A security hot fix or virus scanner may potentially, influence the validated status of a system and lead to unpredictable behaviour. |
No protection against (new) viruses or misuse due to security loopholes. |
|
Risk evaluation |
For security hot fixes, the risk is considered very low, since these usually involve minor changes to the operating system with no influence on the application software. Virus scanners similarly have no direct influence on the application software. In both cases, not implementing the updates exposes the system to considerably higher risk from viruses and security loopholes. |
In the case of a virus attack, uncontrollable damage may result, which can affect GMP-relevant systems. In addition, if the import is delayed, the cause analysis can be difficult or impossible if the system behaves unpredictably. |
|
Risk minimisation |
The procedure for implementing and testing the pattern is described in the IT SOP [...]. Before import, a test of suitable scope is performed and documented within IT. If unexpected behaviour occurs, the reason can thus be easily traced. |
In this case the risk cannot be minimised without importing security hot fixes or virus scanners at the right time. |
The rest consists of a detailed conclusion and signatures, in this case from quality assurance and the decision maker.
|
Conclusion Of the two alternative scenarios, only the first offers the necessary protection against virus attacks that can result in serious damage to the applications and hence to the company. Consequently, the rapid import of security hot fixes and virus scanners is absolutely necessary. In order to reduce the risks in terms of GMP, the test and import should be performed and documented in accordance with specific procedures. This is detailed in the IT SOP [...]. |
After the informal method, the most frequently used methods in the pharmaceutical industry are listed below:
- Fault Tree Analysis (FTA)
- Failure Mode Effects Analysis (FMEA)
- Hazard Analysis and Critical Control Points (HACCP)
These are described in more detail in the following (see chapter 10.E Fault tree analysis (FTA), chapter 10.F Failure Mode Effects Analysis (FMEA) to chapter 10.H Hazard Analysis of Critical Control Points (HACCP)). In contrast to ICH Q9, the methods are described in a different order for the causal sequence described above. This means that we begin with the practical implementation, e.g. with the FTA, and use this as a basis for creating an FMEA or HACCP.
|
Summary Since there is no single method suitable for all application areas, in practice, risk management will always be composed of several methods. In order to keep the training workload to a minimum and to maximise the use of synergies, companies should still limit the number of different methods used (max. 3-4). The methods most commonly applied in the pharmaceutical industry include FMEA, FTA, HACCP and combinations of these methods (see chapter E.8 ICH Q9: Quality Risk Management ). The fishbone (cause-effect diagram) is an appropriate medium for preparation. This brings together all the factors that may have an impact on product quality (manpower, machinery, materials, methods (process), and milieu). The result is an overview of potentially critical influencing variables. The informal method can be universally applied. Since no extensive training is required, it can be very flexibly adapted to the situation to be evaluated. It is primarily used for decision preparation, but in general does not follow a systematic approach. |

